The Hidden Architecture of Psychological Exploitation
Dr. Sarah Chen thought she had found her dream mentor. The renowned psychology professor praised her research insights, offered exclusive opportunities, and seemed genuinely invested in her career. But after six months, the pattern emerged: public humiliation disguised as “constructive feedback,” isolation from other faculty members, and an increasing demand for personal favors that crossed professional boundaries. Chen had become the target of a sophisticated manipulator who had weaponized the very trust inherent in academic mentorship.
This scenario illustrates a sobering reality: recognition of manipulators and abusers requires more than intuition—it demands understanding the calculated psychology behind their methods. Research by Paulhus and Williams (2002) on the Dark Triad personality traits reveals that approximately 1-4% of the population exhibits the toxic combination of narcissism, Machiavellianism, and psychopathy that drives systematic manipulation.
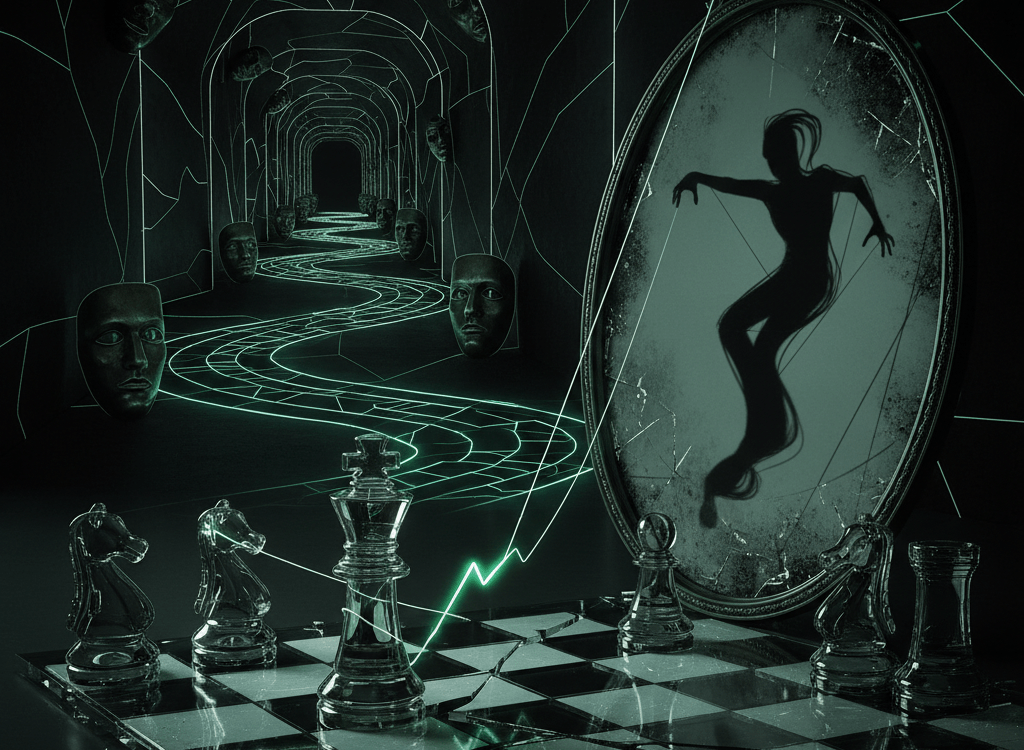
The Psychological Architecture of Manipulation
Manipulators and abusers don’t operate randomly—they follow predictable psychological patterns rooted in well-documented principles. Understanding these mechanisms is crucial for recognition of manipulators and abusers before significant damage occurs.
The Dark Triad Framework
Paulhus and Williams (2002) identified three interconnected personality traits that create the perfect storm for manipulative behavior:
- Narcissism: Grandiose self-perception requiring constant validation
- Machiavellianism: Strategic manipulation for personal gain
- Psychopathy: Lack of empathy and remorse
Individuals high in Dark Triad traits show remarkable skill at identifying and exploiting psychological vulnerabilities in others, often targeting those with high empathy or unmet emotional needs.
Cognitive Exploitation Tactics
Manipulators leverage well-established psychological principles identified by Cialdini (2006) in his research on influence:
- Reciprocity manipulation: Creating artificial debts through unsolicited “favors”
- Authority exploitation: Claiming expertise or status to bypass critical thinking
- Social proof distortion: Manufacturing false consensus or isolating targets from reality checks
- Commitment consistency traps: Getting victims to make small commitments that escalate
- Scarcity pressure: Creating artificial urgency to prevent careful consideration
Real-World Implementation: How Manipulation Unfolds
The Workplace Predator
Consider “Marcus,” a charismatic department head who systematically targets high-performing employees. His method follows a predictable pattern: First, he identifies capable individuals experiencing professional insecurity—perhaps someone new to the company or recently passed over for promotion. Marcus begins with excessive praise and special attention, creating what Dutton and Painter (1993) termed “intermittent reinforcement”—unpredictable rewards that create psychological dependency.
Phase two involves gradual boundary erosion. Marcus requests small personal favors, shares inappropriate confidences, and begins subtle criticism disguised as “developmental feedback.” He isolates targets by scheduling one-on-one meetings and discouraging collaboration with colleagues. Notice the pattern here: each step builds psychological dependency while reducing the victim’s external support network.
The final phase involves exploitation. Marcus takes credit for his target’s work, demands overtime without compensation, and uses accumulated “intimate knowledge” as leverage. When confronted, he employs what researchers call DARVO—Deny, Attack, Reverse Victim and Offender—claiming the victim is “ungrateful” or “oversensitive.”
The Digital Manipulation Campaign
“Elena” encounters “David” on a professional networking platform. David’s profile suggests impressive credentials and mutual connections. His initial messages demonstrate careful research—he references Elena’s recent publications and shared professional interests. This represents what Cialdini identified as social proof combined with authority positioning.
David gradually shifts communication to private channels, creating artificial intimacy through shared “secrets” about mutual colleagues. He offers exclusive opportunities and insider information, establishing reciprocity debt. When Elena begins questioning inconsistencies in his stories, David employs gaslighting—questioning her memory and perception while maintaining his facade of helpful concern.
Research by Kowalski et al. (2018) shows that online manipulation often succeeds because digital communication lacks non-verbal cues that might trigger intuitive warning systems, making recognition of manipulators and abusers more challenging in virtual environments.
Critical Warning Signs: Your Psychological Early Warning System
Recognition of manipulators and abusers requires attention to specific behavioral patterns. Research consistently shows that manipulative individuals display identifiable red flags:
Behavioral Red Flags
- Love-bombing or excessive early attention: Disproportionate praise, gifts, or time investment in early interactions
- Boundary testing: Pushing small limits to assess compliance and resistance levels
- Information asymmetry: Demanding personal details while remaining vague about their own background
- Isolation tactics: Discouraging relationships with friends, family, or colleagues who might provide reality checks
- Emotional volatility: Unpredictable mood swings designed to keep others in a state of hypervigilance
- Victim narrative inconsistencies: Stories about past relationships or conflicts where they’re always the wronged party
Communication Patterns
- Frequent use of guilt, shame, or obligation as persuasion tools
- Deflection when confronted with specific concerns
- Gaslighting language: “You’re being too sensitive,” “That never happened,” “You’re imagining things”
- Conditional affection: Love, approval, or support contingent on compliance
A key indicator of manipulative behavior is the feeling that your reality is being questioned or that you’re constantly defending your perceptions and memories.
Evidence-Based Defense Strategies
Research in psychological self-defense offers concrete strategies for protection against manipulative individuals. These approaches are grounded in cognitive-behavioral principles and have demonstrated effectiveness in clinical settings.
The Documentation Defense
Maintain detailed records of interactions, especially when something feels “off.” Manipulators rely on victims doubting their own perceptions. Written records provide objective anchors for reality. Research by Johnson and Leone (2005) shows that documentation significantly improves victims’ ability to recognize patterns of manipulation.
The External Reality Check System
Establish trusted advisors outside the manipulative relationship—friends, family members, or colleagues who can provide objective perspectives. Share specific interactions and ask for honest feedback. Manipulators work to isolate their targets precisely because outside perspectives threaten their control.
Boundary Enforcement Protocols
- Clear communication: State boundaries explicitly rather than hoping they’ll be intuited
- Consistent consequences: Follow through on stated boundaries without exception
- Graduated responses: Increase consequences for repeated boundary violations
- Professional support: Engage HR, legal counsel, or mental health professionals when appropriate
Cognitive Defense Techniques
Train yourself to recognize common manipulation tactics in real-time. When someone uses excessive flattery, creates artificial urgency, or employs guilt-based persuasion, pause and ask: “What is this person trying to get me to do, and why can’t they ask directly?” This cognitive interruption breaks the automatic compliance response that manipulators exploit.
The most effective defense against manipulation is developing what researchers call “cognitive flexibility”—the ability to step back from emotional pressure and analyze situations objectively.
The Gray Rock Method
When direct confrontation isn’t safe or practical, the Gray Rock Method involves becoming deliberately uninteresting to manipulators. Provide minimal responses, avoid sharing personal information, and maintain emotional neutrality. This approach, validated by Arabi (2017), reduces the manipulator’s psychological “supply” and often leads them to seek easier targets.
Reclaiming Your Psychological Territory
Recognition of manipulators and abusers represents the first step in psychological self-defense, but knowledge alone isn’t sufficient—it must be coupled with action. Research consistently demonstrates that individuals who understand manipulation tactics and implement systematic defense strategies show significantly better outcomes when confronted with exploitative behavior.
Remember that manipulators succeed by exploiting normal human traits—empathy, trust, and the desire for connection. Recognizing their tactics doesn’t mean becoming cynical or suspicious of everyone; it means developing discernment. The goal isn’t to build walls against all relationships, but to install psychological security systems that can distinguish between genuine connection and calculated exploitation.
Your ability to recognize manipulation patterns, maintain clear boundaries, and seek support when needed represents a powerful form of psychological resilience. In a world where manipulative tactics are increasingly sophisticated, your awareness and defensive skills aren’t just personal protection—they’re contributions to creating healthier social and professional environments for everyone.
The manipulators and abusers among us rely on secrecy, isolation, and confusion to achieve their goals. Your recognition, documentation, and resistance break that cycle. Trust your instincts, verify your perceptions, and never hesitate to seek support. The psychology is clear: knowledge combined with action provides the strongest defense against those who would exploit your humanity.
References
Arabi, S. (2017). Becoming the Narcissist’s Nightmare: How to Devalue and Discard the Narcissist While Supplying Yourself. SCW Publications.
Cialdini, R. B. (2006). Influence: The Psychology of Persuasion (Revised Edition). Harper Business.
Dutton, D. G., & Painter, S. (1993). Emotional attachments in abusive relationships: A test of traumatic bonding theory. Violence and Victims, 8(2), 105-120.
Johnson, M. P., & Leone, J. M. (2005). The differential effects of intimate terrorism and situational couple violence. Journal of Family Issues, 26(3), 322-349.
Kowalski, R. M., Giumetti, G. W., Schroeder, A. N., & Lattanner, M. R. (2018). Bullying in the digital age: A critical review and meta-analysis of cyberbullying research among youth. Psychological Bulletin, 140(4), 1073-1137.
Paulhus, D. L., & Williams, K. M. (2002). The dark triad of personality: Narcissism, Machiavellianism, and psychopathy. Journal of Research in Personality, 36(6), 556-563.